The UN voiced alarm Monday at reports that several governments used Israeli phone malware to spy on activists, journalists and others, stressing the urgent need for better regulation of surveillance technology.
Media reports said:
The UN High Commissioner for Human Rights Michelle Bachelet said the apparent widespread use of Pegasus spy software to illegally undermine the rights of those under surveillance, including journalists and politicians, was “extremely alarming” and confirmed “some of the worst fears” surrounding the potential misuse of such technologies.
The reports about the Pegasus spyware “confirm the urgent need to better regulate the sale, transfer and use of surveillance technology and ensure strict oversight and authorization,” UN human rights chief Michelle Bachelet said in a statement.
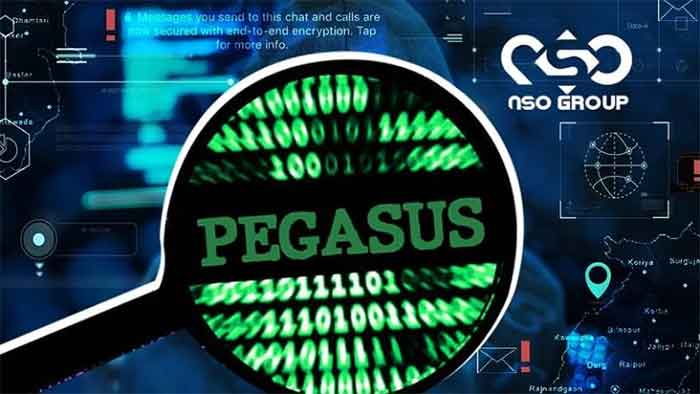
A consortium of collaborative investigation by The Washington Post, The Guardian, Le Monde and other media outlets revealed potentially far more extensive spying than previously thought using the malware from Israel’s NSO Group, capable of switching on a phone’s camera or microphone and harvesting its data.
The use of the ‘Pegasus’ malware to snoop on the phone communications of politicians, journalists, activists and business figures was revealed by French outlet Forbidden Stories and the human rights group Amnesty International. These NGOs obtained a leaked list of 50,000 phone numbers, some of which were allegedly breached by the Pegasus malware, and shared the data with 17 media outlets. Le Monde was one of these outlets, which began publishing stories of the security breaches on Sunday.
Amnesty’s Security Lab conducted a forensic analysis of some of the phones on the list, which was peer-reviewed by Citizen Lab, a group at Toronto University that has been tracking suspected cases of Pegasus infections for years. Of the 67 smartphones analyzed, evidence of successful infection was found on 23 and evidence of attempted infiltration on 14.
A source told investigators that the average number of targets per customer was 112 and that the company had 45 customers for its Pegasus spyware, corroborating the NSO Group’s assessment of the 50,000 figure. Some numbers were landlines that could not be infected by Pegasus at all.
Bachelet described the revelations as “extremely alarming.”
She added that they “seem to confirm some of the worst fears about the potential misuse of surveillance technology.”
She recalled that the UN had repeatedly flagged the dangers of authorities using surveillance tools to hack phones and computers of those legitimate journalists, activists and political opponents in the name of public safety.
“Use of surveillance software has been linked to arrest, intimidation and even killings of journalists and human rights defenders,” she added.
She also warned that broad use of such technologies could lead to self-censorship.
The UN human rights chief said surveillance measures can only be justified “in narrowly defined circumstances, with a legitimate goal” such as “investigations into serious crimes and grave security threats.”
“If the recent allegations about the use of Pegasus are even partly true, then that red line has been crossed again and again with total impunity.”
Bachelet said companies involved in developing and distributing surveillance technologies should ensure their technologies are not used to violate human rights.
She said that states should halt surveillance that violates human rights and protect individuals from companies abusing their right to privacy, including by regulating spying technology.
“Various parts of the UN Human Rights system, including my own Office, have repeatedly raised serious concerns about the dangers of authorities using surveillance tools from a variety of sources supposed to promote public safety in order to hack the phones and computers of people conducting legitimate journalistic activities, monitoring human rights or expressing dissent or political opposition”, said High Commissioner Michelle Bachelet in a statement.
The Pegasus malware infects electronic devices, enabling operators of the tool to obtain messages, photos and emails, record calls, and even activate microphones, according to the investigative report by the media consortium. The leak contains a list of more than 50,000 phone numbers which reportedly belong to those identified as people of interest, by clients of the company behind Pegasus, including some governments.
“Journalists and human rights defenders play an indispensable role in our societies, and when they are silenced, we all suffer”, she said.
Given that Pegasus spyware, “as well as that created by Candiru and others, enable extremely deep intrusions into people’s devices, resulting in insights into all aspects of their lives”, the UN rights chief underscored, “their use can only ever be justified in the context of investigations into serious crimes and grave security threats.”
Companies developing and distributing surveillance technologies are responsible for avoiding human rights abuses, she said, and they must take immediate steps to mitigate and remedy the damage their products are causing, or contributing to, and carry out “human rights due diligence” to ensure that they no longer play a part in “such disastrous consequences” now, or in the future.
States also have a duty to protect individuals from privacy rights abuses by companies, she added.
One key step in this direction is for States to require by law that the businesses meet their human rights responsibilities by becoming more transparent in their design and use of products and by putting in place effective accountability mechanisms.
Governments should not only immediately stop using surveillance technologies in ways that violate human rights, but also “take concrete actions” to protect against such invasions of privacy by “regulating the distribution, use and export of surveillance technology created by others”, the High Commissioner said.
Without human rights-compliant regulatory frameworks, Ms. Bachelet upheld that there are “simply too many risks” that the tools could be used to intimidate critics and silence dissent.
Morocco Spied on French President Macron with ‘Pegasus’
The Moroccan government used Israeli malware to spy on French President Emmanuel Macron’s phone calls, Le Monde has reported. More than a dozen other French politicians were reportedly targeted in a scheme denied by Morocco.
Hours after Paris prosecutors launched an investigation into allegations that Morocco’s intelligence agencies used Israeli malware to hack the phones of several French journalists, Le Monde reported that Macron was also targeted by Rabat’s agents in 2019, along with former Prime Minister Edouard Philippe and 14 other ministers.
“If the facts are true, they are obviously very serious,” Macron’s office told Le Monde on Tuesday, promising that “all light will be shed on these revelations.”
On Monday, the Moroccan government denied any use of the Israeli spyware, calling the accusations by Le Monde and others “unfounded and false.”
Morocco “never acquired computer software to infiltrate communication devices,” read a statement from the government, which denied that it had “infiltrated the phones of several national and international public figures and heads of international organizations through computer software.”
Macron is not the only high-level political figure allegedly surveilled. Mexican President Andres Manuel Lopez Obrador was reportedly spied on by the administration of his predecessor, President Enrique Peña Nieto.
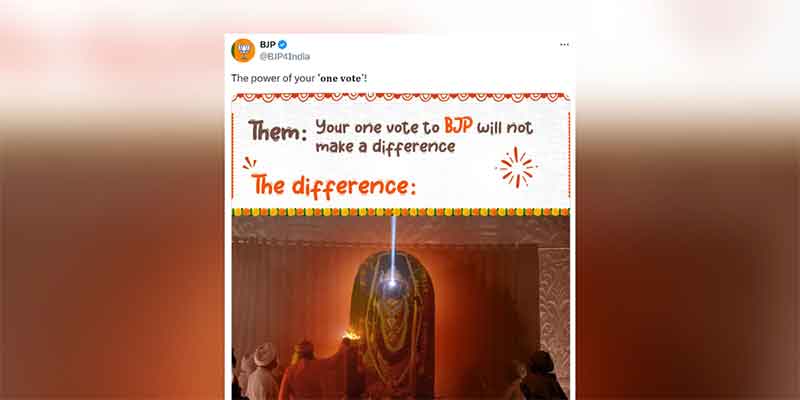
According to media reports, Hungarian Prime Minister Viktor Orban also potentially used Pegasus to spy on a political opponent, as did Indian Prime Minister Narendra Modi.
The Paris prosecutor’s probe will consider 10 possible charges, including potential breaches of personal privacy and fraudulent access to personal electronic devices.
The surveillance-revelation was followed by a legal complaint filed by French outlet Mediapart, which claimed that Morocco’s secret services used Pegasus to spy on two of its reporters.
Another French outlet, Le Canard enchaine, is reportedly preparing to follow suit with similar allegations.
A leaked list of alleged Pegasus targets included 50,000 telephone numbers belonging to journalists, businessmen, NGO workers, religious leaders and even presidents and prime ministers. Dating back to 2016, the list was reportedly compiled from requests from NSO clients in 10 countries: Azerbaijan, Bahrain, Hungary, India, Kazakhstan, Mexico, Morocco, Rwanda, Saudi Arabia and the United Arab Emirates (UAE). Hungary has also denied the claims, and NSO said that the alleged leak has been mischaracterized by media reports.
France is not alone in seeking answers about the purported spying scandal. Indian lawmakers on Tuesday called for a parliamentary investigation into the government’s alleged use of Pegasus.
Amazon Cuts Business Ties with NSO Group
Amazon has pulled the plug on infrastructure and other services that it offered to Israeli surveillance firm NSO Group, following allegations that the company’s spyware was being used to snoop on journalists and activists.
The tech and retail giant announced on Monday that it had deactivated cloud computing accounts linked to NSO Group. The Israeli company reportedly used Amazon Web Services (AWS) to operate the spyware programs that it marketed to governments around the world. The move comes after Amnesty International’s Security Lab conducted a forensic analysis of telephones on a leaked list of targets for NSO’s flagship malware, Pegasus.
NSO Group disputed that AWS had shut down its accounts, prompting Amazon to double down.
Amnesty also claimed that NSO’s malware sent information “to a service fronted by Amazon CloudFront, suggesting NSO Group has switched to using AWS services in recent months.”
Citizen Lab said in a peer review of Amnesty’s finding that it had “independently observed NSO Group begin to make extensive use of Amazon services including CloudFront in 2021.”
CloudFront is an Amazon service that allows clients to securely deliver data using high transfer speeds.
While Amazon rushed to cut ties with NSO, it was less proactive when media reports revealed in May 2020 that the Israeli firm may have used Amazon infrastructure to deliver malware to unsuspecting victims. At the time, the company failed to respond to a request for comment asking if NSO had breached Amazon’s terms of service.
Journalists, ministers, Khashoggi’s son and a ruler’s family possible targets for Pegasus
Among the people presumed to be selected for digital surveillance are “hundreds of business executives, religious figures, academics, NGO officials, union officials and government officials, including cabinet ministers, presidents and prime ministers,” The Guardian reported. It also includes “close families members of one country’s rulers, suggesting the ruler may have instructed their intelligence agencies to explore the possibility of monitoring their own relatives.”
The Israeli firm rejected that its malware was in any way implicated in the assassination of Jamal Khashoggi, a self-exiled columnist for the Washington Post, who was killed at a Saudi consulate in Istanbul in October 2018 in what many believe was a government-sponsored murder. Riyadh blamed it on a rogue group of security agents, who were tried and sentenced for the killing. The phone of Khashoggi’s fiancee was penetrated by Pegasus just four days before his death, while the phones of his son, other family members, friends, and coworkers were found on the presumed list of targets, the investigators said.
NSO Group said that its “technology was not associated in any way with the heinous murder” of Khashoggi and was not used to “listen, monitor, track, or collect information regarding him or his family members” mentioned in an inquiry sent to the company.
Clients in Mexico selected the most numbers – more than 15,000 – followed by Morocco and the UAE, each with more than 10,000 numbers.
The investigators promised a number of publications based on their analysis to be released in the coming weeks. On Sunday, The Guardian also printed a look at journalists on the list, an expose of alleged use of Pegasus by the Hungarian government, and a story about Mexican investigative journalist Cecilio Pineda Birto.
Birto’s March 2017 murder was long alleged to be linked to a Pegasus surveillance operation. His phone number was also among the presumed hacking targets. The software location-tracking features may have helped his killers to find him, investigators suspect.