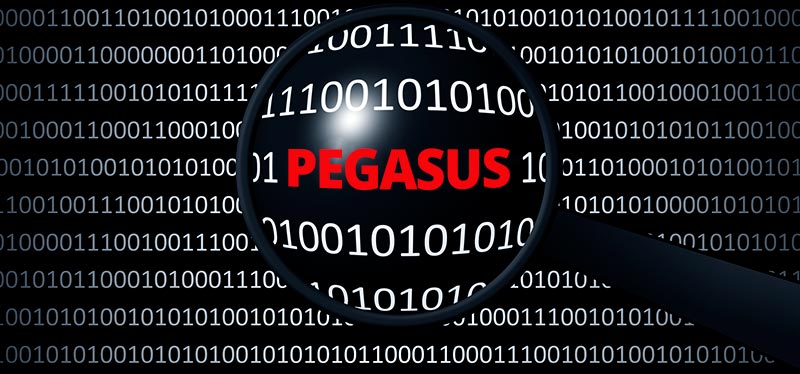
In a detailed report released today, 17th December, 2021, Arsenal Consulting, the Boston-based forensic investigation firm assisting the defense lawyers in the Bhima Koregaon (BK) case, and Amnesty Tech Security Lab, have confirmed that the iPhone of one of the key accused, Mr. Rona Wilson, was attacked multiple times by the Pegasus spyware. This has been simultaneously reported in the Washington Post and The Wire.
The present report identifies 49 different instances of Pegasus attack, and sometimes of successful infection, on Mr. Wilson’s iPhone, between July 5, 2017 and April 10, 2018. This is striking given that Arsenal’s previous reports had already shown that Mr. Wilson’s computer had been hacked by the NetWire Remote Access Trojan (RAT) between June 13, 2016 and April 17, 2018 – covering the same period – in order to plant incriminating files on his computer. The same had been done to the computer of another accused in the Bhima Koregaon case, Surendra Gadling. Arsenal also confirmed that neither Mr. Wilson nor Mr. Gadling had ever opened the incriminating files in question.
Thus, in 2017 and 2018, Mr. Wilson was being subjected to both surveillance through Pegasus and evidence planting through the NetWire RAT.
In the Bhima Koregaon case, sixteen leading human rights defenders, lawyers, scholars, and artists have been jailed without trial for over three years under the draconian Unlawful Activities (Prevention) Act (UAPA). Speaking for the defense team, advocate Mihir Desai said that “the dual attack on Mr. Wilson’s computer and phone over a period of two years is not just alarming, but something that should remind every democratic institution that illegal cyber – attacks can turn innocent citizens into alleged criminals who can then be jailed indefinitely.”
The publication of this report raises three extremely critical and troubling questions:
1. It is now over 300 days since the first report revealing the NetWire attack and evidence-planting and nearly 150 days since the reports on the Pegasus attacks. Together this is the single best-documented case of a cybercrime compromising India’s criminal justice system and the rights of its citizens. Yet the government remains silent. Why?
2. Simple due diligence after these reports should have compelled the NIA to re-examine the devices of those it has accused of terrible crimes and publish its findings. Ordinary anti-virus software can detect NetWire malware, and Amnesty International Security Lab has documented how to identify Pegasus attacks and infections. If the NIA does not even care to investigate these aspects, how can it claim its actions are legitimate?
3. The first Pegasus attack on Mr. Wilson’s iPhone took place on the second day of Prime Minister Modi’s visit to Israel where the NSO group company that manufactures Pegasus, is headquartered. Was this just a coincidence? NSO has repeatedly stated that it sells Pegasus only to governments, and all its sales are subject to approval by the Israeli government. Were there members of the PM’s team who could have been authorized to act on behalf of the government to contract the services of the NSO group and/or authorize attacks on Indian citizens? Or were there any private cyber-security actors, including cyber-security firms with whom the government contracts, who were part of the delegation? Why has the government maintained a studied silence on these questions?
Background:
On July 20 of this year, The Wire and the Washington Post had revealed that eight of the BK accused including Mr. Wilson, as well as several members of their families and friends, had potentially been attacked by Pegasus. However as the device in question − Mr. Wilson’s iPhone − is in the possession of the NIA, this could not be confirmed. Arsenal’s subsequent investigation instead examined the iTunes backups of his phone on Mr. Wilson’s hard drive and found that his phone had indeed been attacked. Arsenal’s results were verified by Amnesty International Security Lab, which had developed the primary techniques to identify Pegasus attacks and infections.
Given that we now have compelling evidence that there are citizens who’ve been attacked by both Netwire and Pegasus, it is crucial that the committee appointed by the Supreme Court investigate any connections between the two attacks and the implications for the BK case. The four reports from Arsenal taken together leave little doubt that the BK case has no evidentiary basis. At the minimum, all the accused must be granted bail immediately. We hope that the judiciary will take note of the fact that electronic evidence can be falsified and tampered with and that there is need to develop new evidentiary principles and approach to deal with electronic forensic investigatory reports like the Arsenal Report.
V. Suresh, National General Secretary, People’s Union for Civil Liberties, (PUCL)